What is Zero Trust in Cyber Security?
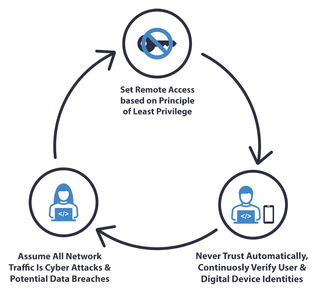
The Zero Trust approach in cybersecurity is a security model that requires all users, devices, and applications to be authenticated and authorized before being granted access to an organization's resources.
A zero-trust environment does not make any assumptions about the trustworthiness of users. Instead, it uses a "least privilege" approach in which users are only given the least privilege access that they need to do their job and no more. This approach can help organizations improve their cybersecurity posture by making it more difficult for attackers to access sensitive data. It also simplifies security management by eliminating the need to manage complex firewall rules.
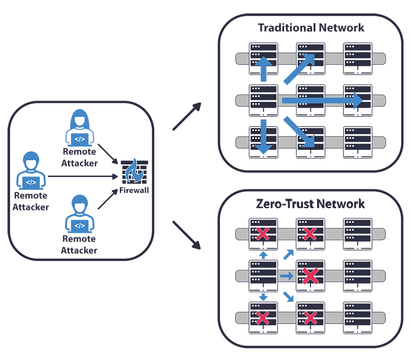
While in a traditional trust-based environment, organizations typically have perimeter-based security that relies on firewalls and other security controls to keep the bad guys out.
Zero trust environments are often considered more secure than traditional trust-based ones, but some tradeoffs must be considered. For example, zero trust environments can require more effort to set up and manage and may not be compatible with all legacy applications.
In a nutshell, ZERO TRUST MODEL refers to a method of data protection that does not depend on predetermined trust levels. Instead, every person and piece of hardware is assumed to be malicious until proven otherwise.
History of Zero Trust Security
- Pre-2004 Era: The perimeter-based approach had been the standard security posture for decades. The enterprise adoption of cloud computing began to tear down the perimeter-based system in the first two decades of the 21st century. The defensive posture of enterprise security teams had to be rethought due to this transition.
- The Idea of Zero Trust took hold in 2004: Although the concept of Zero Trust had its beginnings before 2004, the actual foundation of the Zero Trust framework was laid in 2004 when the Jericho Forum, an international security consortium, presented concepts. He saw potential issues with the perimeter defence strategy and developed a new security concept called deperimeterization. Encryption and data-level authentication were two examples of the multiple security controls suggested by this concept.
- In 2010, the term "Zero Trust" was born: "Zero Trust" was first coined by John Kindervag, the principal analyst at Forrester Research 2010. He proposed the Zero Trust model as an alternative to the traditional perimeter-based security approach.
The perimeter-based approach relies on predefined implicit trust levels—you're either inside the perimeter and trusted or outside and untrusted.
Kindervag argued that this approach is no longer effective in today's networked world. With more employees working remotely and using personal devices, it's become impossible to draw a clear line between insiders and outsiders. And as data moves freely across borders, it's also become more difficult to protect data within physical perimeters.
How Does the Zero-Trust Security Model Work?
NEVER TRUST UNTIL VERIFIEDAccording to the Zero Trust strategy
1. Continuous monitoring and validation
Continuous monitoring and validation are essential to the success of any zero-trust strategy. By continuously verifying the identity of users, devices, and applications, you can ensure that only authorized users can access corporate data and resources. Additionally, by constantly monitoring activity on your network, you can quickly detect and respond to any suspicious activity.
Implementing a continuous monitoring and validation strategy can be challenging, but there are a few best practices that can help:
- Use multiple layers of authentication, such as two-factor or biometric authentication, to verify users' identities.
- Grant role-based data access to users so that they access only the data they need for their job function.
- Monitor activity on your network in real-time so you can quickly identify and respond to any suspicious activity.
- Use application whitelisting to restrict which applications can be run on corporate devices.
By following these best practices, you can improve your chances of success with any zero-trust strategy.
2. Least privilege
In cybersecurity, the least privilege is granting limited access to data and systems to only those subjects who require it to do their job tasks. The idea is that if users only have access to the resources they need, they cannot accidentally or maliciously misuse or damage them.
Least privilege is a fundamental security principle that can be applied to individual users, groups of users, and even entire organizations. When properly implemented, it can help reduce the risks associated with data breaches, malware infections, and other cybersecurity threat
3. Multi-factor authentication (MFA)
MFA is essential to Zero Trust security because it adds an extra layer of protection. If one factor is compromised, the attacker must still get past the other factors to gain access. This makes it much harder for attackers to breach your systems successfully.
There are many different ways to set up MFA, so you can choose the method that best suits your workload security needs. For example, you require users to enter a one-time code from their mobile app every time they log in. Alternatively, you may set up biometric authentication so that only authorized users can access certain system
4. Microsegmentation
Microsegmentation is a security strategy that involves dividing a network into smaller segments, or microsegments, and then applying security controls to each element.
- Micro-segmentation aims to limit the spread of malware or other malicious activity within a network by isolating each segment from the others.
- Microsegmentation can be accomplished in several ways, including:
- Physical segregation (such as using separate LANs for different segments)
- Logical segregation (such as using VLANs)
- Software-defined networking (SDN)
SDN allows for more granular control over network traffic and can be used to create virtual micro-segments isolated from one another.
5. Data encryption:
Encrypting data at rest and in transit helps protect it from being accessed by unauthorized individuals, even if they can gain access to the network itself.
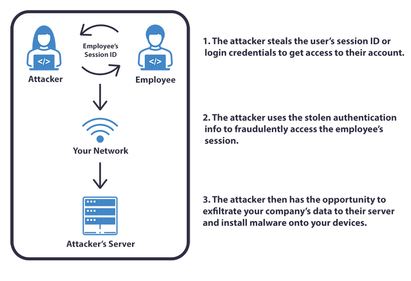
6. Preventing lateral movement
This is one of the critical components of a Zero Trust Network. Lateral movement is when a hacker gains access to one system and then uses that system to gain access to others on the network. By preventing lateral movement, organizations can make it much harder for attackers to compromise their systems.
History of times when implementing zero trust network access could have helped with a network breach?
Using Zero Trust security principles might have reduced the number of high-profile data breaches in recent years. Some instances are as follows:
- Equifax data breach: Almost 143 million people's personal information was compromised due to a severe data security breach at Equifax in 2017. Hackers gained access to the system because they found and exploited a flaw in a web application. If Equifax had used a zero trust strategy, it would have been more challenging for the attackers to access sensitive data since it would have been limited based on the user's identity, device, and behaviour.
- Target data breach: It occurred in 2013, and as a result, the credit card details of approximately 40 million consumers were compromised. The hackers could access Target's payment system and steal credit card information using the vendor's credentials. If Target had used a zero-trust strategy, the vendor's access to the company's payment system might have been limited based on the vendor's identity, device, and activity, making it more difficult for the attackers to use the vendor's credentials to get access to Target's payment system.
- OPM data breach: Information of more than 21 million current and past federal workers was compromised due to a data breach at the Office of Personnel Management (OPM) in 2015. The hackers breached the OPM network using the credentials of a third-party contractor. With a Zero Trust approach, the contractor's access to OPM's network could have been restricted based on the contractor's identity, device, and behaviour, making it more difficult for the attackers to use the contractor's credentials to access OPM's private network itself.
- Yahoo data breach: Yahoo is the unlucky victim of not one but two of the most significant data breaches ever recorded. In 2013, three billion people had their account information, including unencrypted security questions and answers, compromised. Around 500 million accounts were compromised a year later. Compromised information included full names, dates of birth, email addresses, encrypted passwords, and answers to secret questions.
A Zero Trust approach could have helped prevent or mitigate these data breaches by restricting or granting access to sensitive data based on user and device identity, device state, and behaviour rather than relying solely on perimeter-based security measures.
Zero Trust use cases
Here are five examples where Zero Trust security policies can significantly bolster a company's security posture.
- Remote Access: With the rise of remote work, many organizations are using Zero Trust to secure remote access to corporate resources. Instead of relying solely on a VPN, Zero Trust network access solutions use multi-factor authentication, access controls, access policies and continuous verification to ensure that only authorized users and devices can access corporate resources on the network.
- Privileged Access: Many cyber attacks involve compromising privileged accounts with access to critical systems and data. Zero Trust solutions can help secure privileged user and device access by implementing access controls, continuous monitoring, and behavioural analytics to detect and prevent unauthorized access.
- Cloud Security: As more organizations move their workloads to the cloud, they face new security challenges. Zero Trust solutions can help secure cloud environments by implementing access controls, encryption, and continuous monitoring to ensure that only authorized users and devices can access cloud resources.
- Insider Threats: Insider threats are a primary concern for organizations, as they can cause significant damage to the business. Zero Trust solutions can help mitigate the risk of insider threats by implementing access controls, continuous monitoring, and behavioural analytics to detect and prevent unauthorized access requests and suspicious activity.
- IoT Security: The Internet of Things (IoT) has introduced new security challenges, as many IoT devices are vulnerable to cyber-attacks. Zero Trust solutions can help secure IoT devices by implementing access controls, encryption, and continuous monitoring to ensure that only authorized devices can access the network.
Zero Trust can be applied to various use cases to help organizations secure their networks, data, and applications. It is a holistic and dynamic security model that requires ongoing monitoring and risk assessment to remain effective.
How to Implement Zero Trust in Businesses?
Implementing a zero-trust model in businesses requires a comprehensive approach that includes the following:
1. Build a Dedicated Group
As your IT staff already has a full plate, they may not prioritize switching to a zero-trust security architecture. The transition to a zero-trust architecture should be planned and carried out by a zero-trust transition team that is relatively modest in size and scope. It is necessary to include professionals knowledgeable in risk management, security operations, application, data, user, and device security.
2. Map Hybrid Environment
Initially, you should check various use cases and draw up a map of hybrid settings. In this way, security teams may more quickly locate possible cyberattack vectors and reduce their vulnerability to such attacks. It is crucial to remember that your zero-trust solution will be useless if you don't have a clear picture of the organization's present security posture. So, it is crucial to have a professional team create an environment map for you.
3. Identify High-Impact Process Flows
Identifying critical process flows is crucial, given the growing difficulty of setting up a secure base for a digitally transformed infrastructure. By examining the process flows and pathways that connect people, devices, applications, and services, dedicated zero-trust teams may be better able to design rules and regulations and acquire the proper tools for enforcing them.
Users should only have secure access to the information and applications they need to do their tasks. Still, the enterprise's efforts to improve its security shouldn't come at the expense of the user experience.
To reduce their vulnerability to cyber attacks, businesses can use access management solutions to identify crucial process flows and implement the least-privileged-access methodology. They can do this without negatively affecting the user experience.
4. Establish Regulations for the Micro-Perimeter
The professional teams can construct the protected surface once they have identified all pathways and process flows. For instance, they may establish perimeter rules and policies to regulate the operation of the network. In this way, businesses can attain finer granularity across all endpoints. The zero-trust security model will scrutinize the most minor possible attack vectors by default.
After identifying the protected surface, it is recommended to position user access and security controls near the attack surface as practicable. Zero-trust teams can construct a micro-perimeter in this manner, which consists of restricted policy statements that are specific and straightforward to comprehend.
5. Deploy a Next Generation Firewall
Your zero-trust strategy would be incomplete without a next-generation firewall. It will function as a micro-segmentation gateway, erecting a small wall around the protected surface. This strategy helps implement additional layers of zero trust concepts, network access control, and a comprehensive examination of traffic attempting to access network resources inside the micro-perimeter.
6. Conceive a Solid Zero-Trust Policy
As soon as the zero-trust network security team has finished designing the first network infrastructure, it may move on to creating and enforcing zero-trust regulations. To decide which resources should be granted unrestricted access, the Kipling Method is widely regarded as the gold standard.
The "who, what, when, where, why, and how" are the central focus of the Kipling Method. For this reason, you should ask something like:
- Who is allowed to use which resources?
- What time frame do they have to use the tool?
- Where does the packet need to go?
- How does the packet get to the protected surface?
- Which programs should workers use to get to data protected by the micro-perimeter?
The Kipling Technique guarantees that only trusted data and programs are allowed via the network.
7. Zero-trust Architecture Must Be Constantly Monitored And Enforced
With the threat landscape constantly shifting, this is the only way businesses can protect their critical assets and data. Due to the impossibility of human beings maintaining constant vigilance and monitoring traffic around the clock, innovative AI and ML-powered technologies are essential. These powerful resources will strengthen business infrastructure and immediately notify security professionals of any threats.
Security information and event management (SIEM) technologies can help zero-trust teams understand security events in their entirety.
8. Establish And Sustain a Safe And Responsible Work Environment
All parties involved must work together to implement the zero-trust approach. The most effective strategy for zero trust principles is bringing security and non-security-oriented teams together to investigate and repair security holes. Businesses can take zero trust initiatives to prevent catastrophic security incidents by identifying and fixing vulnerabilities before threat actors exploit them.
Zero Trust V/S Traditional Trust-based Environments
The traditional trust-based approach to cybersecurity assumes that everything inside the network perimeter can be trusted by default. This approach is based on the belief that solid perimeter defences, such as firewalls and intrusion detection systems, are sufficient to keep cyber threats out. However, as cyber threats have become more sophisticated, this approach has become less effective.
In contrast, the Zero Trust approach assumes no user or device can be trusted by default to gain access anywhere, even inside the network perimeter. It requires continuous authentication and authorization checks for every user, device, and application that tries to access the organization's resources. This approach is based on the principle of "least privilege," which means that users and devices only have access to the resources they need to do their jobs.
Here are some key differences between the Zero Trust initiative and the traditional trust-based approach to cybersecurity:
Perimeter-based vs. User-based
The traditional trust-based approach is perimeter-based, meaning it focuses on protecting the network's perimeter. The Zero Trust approach is user-based, meaning it focuses on verifying the identity of the user or device trying to access the network, regardless of where they are located.
Default trust vs. Continuous verification
The traditional trust-based approach assumes that everything inside the network perimeter can be trusted by default. The Zero Trust approach assumes that no user or device can be trusted by default and requires continuous verification of every user, device, and application that tries to access the network.
Wide access vs. Least privilege
The traditional trust-based approach often grants wide access to network resources by default. The Zero Trust approach is based on the principle of least privilege, which means that users and devices only have access to the resources they need to do their jobs.
Reactive vs. Proactive
The traditional trust-based approach is reactive, focusing on responding to cyber threats after they have breached the perimeter. The Zero Trust approach is proactive, focusing on preventing cyber threats from accessing the network in the first place.
Conclusion
Adopting a zero trust security strategy can offer numerous benefits for organizations, including improved protection against cyber threats, reduced reliance on legacy security solutions, and increased agility.
Implementing a zero-trust model requires a comprehensive approach that includes identification and authentication, continuous monitoring, granular access control, and multi-factor authentication. Businesses can significantly enhance their cybersecurity and protect their sensitive data and assets by taking these steps.
Discussions and Comments
Click here to view and join in on any discussions and comments on this article.

